Generate a report with charts and statistics about cracked passwords in XLSX format
Introduction
•
Authors
•
Features
•
Usage
For more information check out this article
During our assessments, it's common to get our hands on some hashed passwords, often related to an Active Directory (AD) domain. A password dump is usually obtained after compromising a domain controller and it contains the password hash of every account configured in the domain. In the Windows AD case, this hash is usually an NTLM hash, which doesn't offer strong protection against brute force and dictionary attacks.
At this stage, we usually start a password cracking attack on the dumped hashes to assess the strength of the passwords used to access the domain's accounts. And guess what? Users' passwords are usually weak!
This step allows us to get an overview of both the effectiveness of the password policies implemented in the domain and the awareness on the importance of strong passwords. We believe that this information is crucial to assess the security of an organization and, if presented correctly, it can have a significant impact on improving its security posture. However, the critical point is to present the results of this analysis in the best way possible.
First of all, we need to avoid giving the chance of blaming the users or, even worse, finding a scapegoat to blame for the analysis results. The focus should always be on password policies and the importance of security awareness in the employees, never on single cases. For this reason, we anonymize the report, excluding any information that would allow identifying the users.
Then, we need to show the impact of the analysis. Indeed, the list of cracked passwords doesn't provide a lot of information and it is not very useful by itself. For this reason, we need to aggregate the results and extract some useful statistics.
To speed up and standardize this process we developed Kraken. Even if Kraken is designed to integrate with the workflow that we usually follow in this type of activity on Windows AD, it could also be used for similar activities that require password cracking (e.g. Azure AD, LDAP) with minor modifications.
- Maurizio Agazzini, Principal Security Analyst at HN Security
- Stefano Alberto, Security Analyst at HN Security
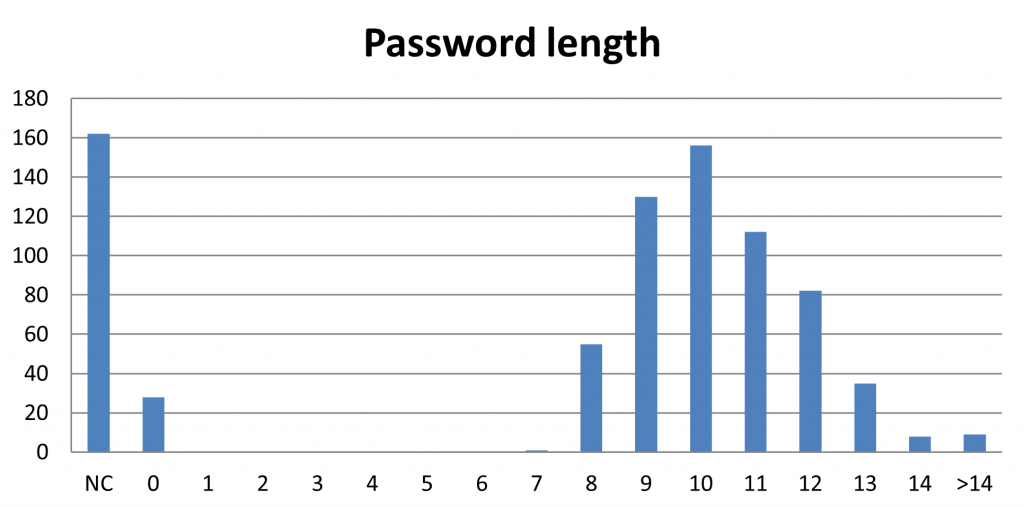
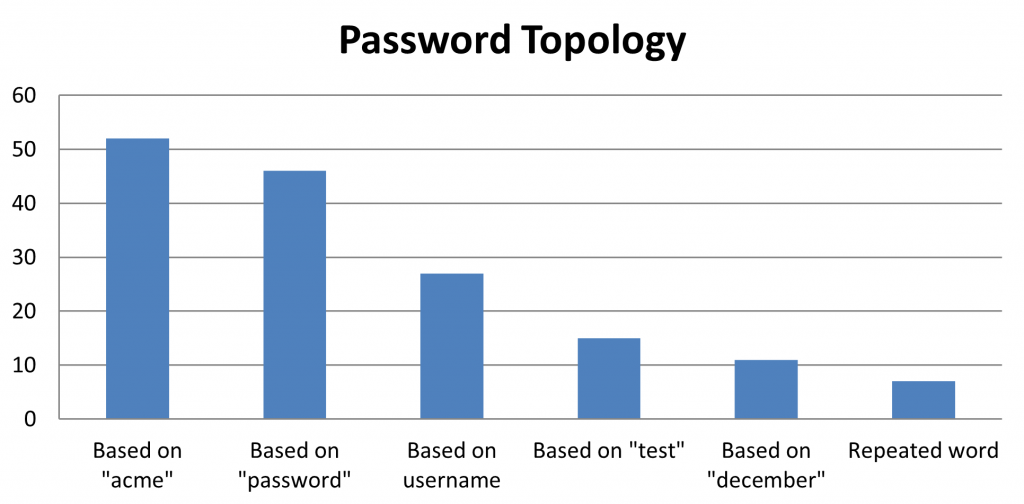
Kraken performs different types of analytics to visualize the results from different points of view, trying to identify patterns in the provided data. We will now take a brief look at the charts automatically generated by Kraken.
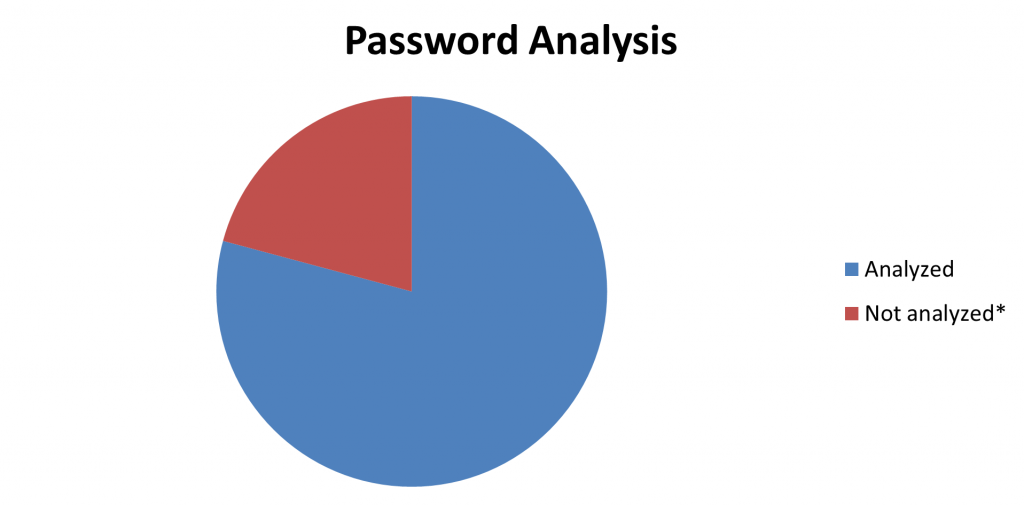
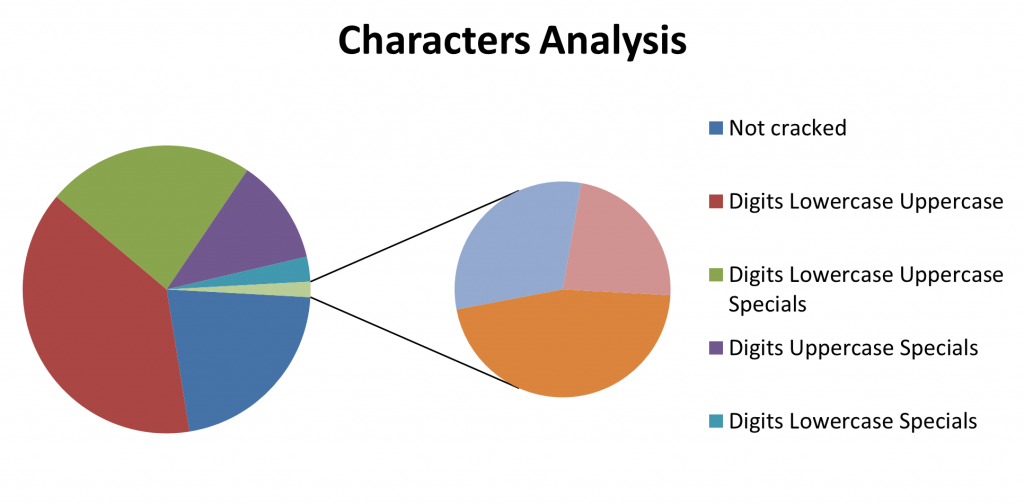
This chart is pretty simple, yet crucial in understanding the impact of the analysis. It shows how many of the passwords we were able to crack, giving an immediate idea of the overall security posture. In this step we analyze the charset used in the cracked passwords. This is important to show potential flaws in the implemented password policy. If we can identify a prevalence of passwords that are based on small charsets we should probably consider implementing a more strict password policy. However, this chart should be interpreted carefully, knowing that it's biased because we are considering only the passwords that were successfully cracked. To address this bias, you can also include the not-cracked passwords in this chart by using theshow-not-cracked option.
show-not-cracked option can be used.
dictionary and the regex options.
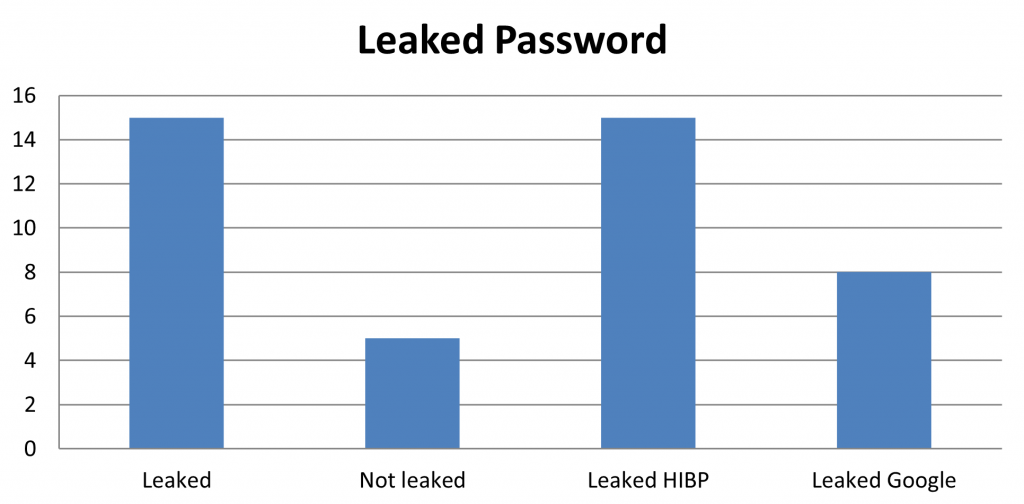
haveibeenpwned
This API offered by haveibeenpwned checks for the presence of the password in a database with hundreds of millions of real-world passwords previously exposed in data breaches.
Google password manager
This service checks for the user and password pair inside a database of leaked credentials. For more information about the design of this API, you can check out this blog post by Google.
This service is freely available to Google Chrome users. However, the API specification is not publicly available. To overcome this limitation we reverse-engineered the protocol to implement it in our tool.
Note that we need a token to use this API. To extract a valid token, the tool will spawn an instance of Google Chrome. You will need to be logged into the browser with a Google account to generate the token. We only use the token to emulate the requests generated by the browser to check the cracked passwords in the data breaches. However, we suggest using a secondary account for this purpose, to avoid any problems with your main Google account. To avoid launching the browser every time, the tool will save the token in the refresh_token file. If this file is found, the tool will check for the validity of the token, reusing it when possible.
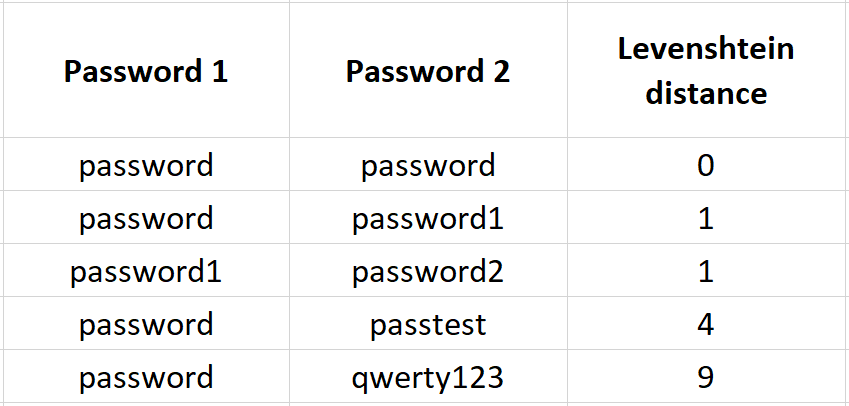
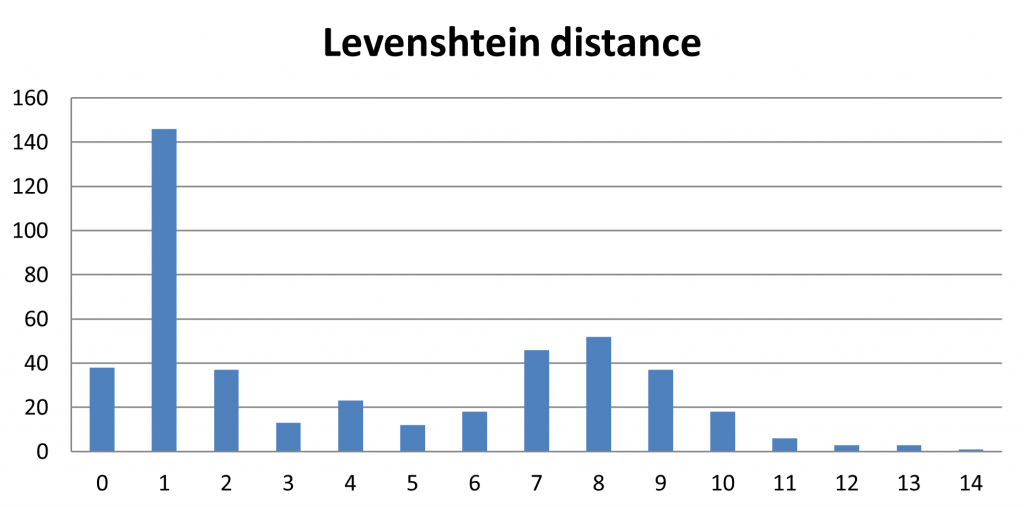
The Levenshtein distance is perfect for this purpose as it measures the "distance" between two strings. A low Levenshtein distance value means that the two strings are very similar to each other, while a high value means the opposite. To better understand this distance definition here are some examples:
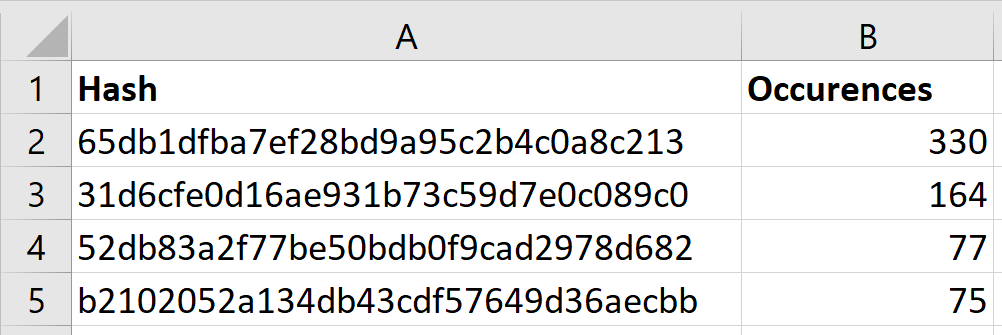
Similarly to the common password ranking, in this case, we rank the most common password hashes. This allows us to identify common passwords that we weren't able to crack that could add more information to the previous analysis.
Kraken is pretty straightforward to use, but, at the same time, it allows customizing the report case by case.
In the most basic case, the tool takes the cracked password file as input and generates the report in the XLSX format. You can try it out with the following command.
python kraken.py --pwd passwords.txt --out report.xlsx
username:password user2:p4ssw0rd anotheruser:$HEX[706124243a776f726421]Note that the tool also supports the process of historical password data. Previous passwords are identified by appending to the username the suffix
_history and an incremental number. For example, this file contains the password history for the user username.
username:currentpassword username_history0:previouspassword username_history1:oldpassword
- Customize what users to consider in the statistics without needing to modify the password file. In this way, we can limit the analysis to a group of users that we are interested in, ignoring the accounts that are not relevant to our purposes.
- Adding the information about all the accounts defined in the domain, even the ones that we weren't able to crack.
This option can be passed to the tool with the syntax --group user_file.txt where each line of the user file is a username that we want to consider in the analysis, as in the following example:
user user1 user2
You can toggle this flag by adding the --show-not-cracked option to the command.
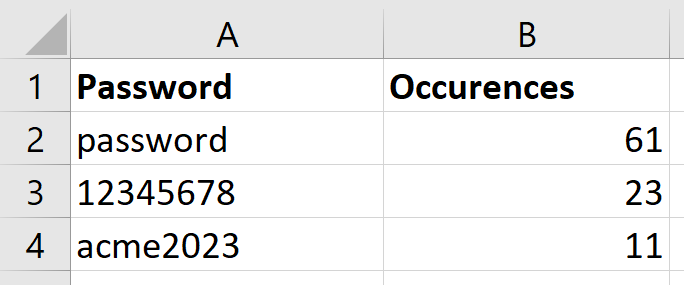
To check if a password is based on a specific word, we consider it case insensitive and we also consider substitutions of letters and numbers (leet). For example, if we added the word "password" in the dictionary all of the following strings will match it and will be categorized based on the word "password":
- password123
- aaaPassWOrd!
- p4ssw0RD?
--dictionary dictionary_file. Each line of the dictionary file contains a word that we want to use to categorize passwords, as in the following example:
acme 2023 password
For example, if we want to highlight the passwords containing a date we could use a regex similar to .\d{8}.. This regex would match all of the following passwords:
02121999 test06072022 tt00000000!
To use this option we can pass it to the tool with the syntax --regex regex_file.txt. Each line of the regex file contains a python regex that will be used to match the cracked passwords, as in the following example:
p(a|4)s.+rd
.*\d{6}.*
You can pass this option with the syntax pwdump hash_dump_file.txt. The file format expected by Kraken is the output format of secretsdump.py. An example of this file format is the following:
octagon.local\Administrator:500:aad3b435b51404eeaad3b435b51404ee:c8ca0f8d1f3ca975464bee8843bceda3::: Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0::: krbtgt:502:aad3b435b51404eeaad3b435b51404ee:52db83a2f77be50bdb0f9cad2978d682::: octagon.local\REVA_JOYCE:1103:aad3b435b51404eeaad3b435b51404ee:b2102052a134db43cdf57649d36aecbb::: octagon.local\MARYANN_HANSON:1104:aad3b435b51404eeaad3b435b51404ee:57cbd01ad63e05402db21fb22cdedda2::: octagon.local\MICHELLE_WOLF:1105:aad3b435b51404eeaad3b435b51404ee:65db1dfba7ef28bd9a95c2b4c0a8c213:::
You can enable this analysis using the haveibeenpwned API by adding the flag --check-leaked in the command.
If you also what to enable the API used by Google password manager you can add the --check-leaked-google flag too.