This project is a Azure DevOps task that allows users to integrate Owasp Zap security analysis into their VSTS pipelines.
Follow the instructions below to add and configure the Owasp Zap Scanner in your build/release pipeline.
- You need to have OWASP Zed Attach Proxy installed (e.g., on onpremise or on a virtual machine) and exposed so it can be accessed over the internet. The following article Installing & Configuring Owasp Zap on an Azure Virtual Machine provides a detailed guide on how to do it.
- Obtain the API Key required to access the ZAP API by following the instructions on the Official Documentation.
Install the Owasp Zap Scanner in your Visual Studio Team Services account and search for the task in the available tasks. The task will appear in the Test section of the task list. Add it to your build/release task.
- ZAP API Url : The fully qualified domain name (FQDN) with out the protocol. (Eg. zap.example.com)
- API Key : The API key for ZAP. Details about obtaining the API can be found on the Official Documentation
- Target URL : Target URL where the active scan is performed against.
- New Session : Creates a new session, optionally overwriting existing files. If a relative path is specified it will be resolved against the 'session' directory in ZAP 'home' dir.
- New Context : Create a new Context, optionally.
This configuration section includes the parameters that need to be sent to perform the active scan against the target.
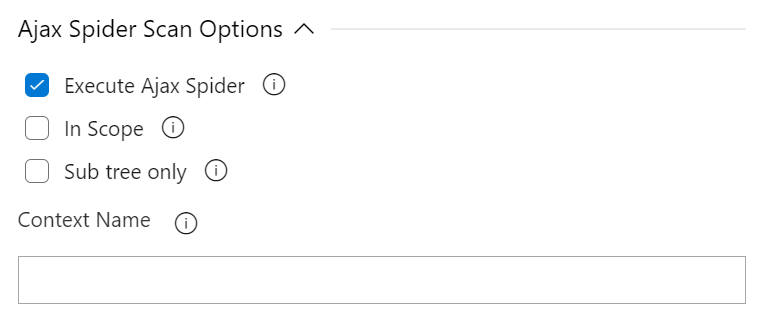
- Execute Ajax Spider Scan : Enable to run a spider scan on the target.
- Subtree Only : (Optional) A boolean (true/false) indicating whether or not the crawl should be constrained to a specific path (default value is false). Enable to use the nodes underneath the one specified target to seed the Ajax spider.
- in Scope : (Optional) A boolean (true/false) indicating whether or not the scan should be restricted to 'inScope' only resources (default value is false). Enable to use the nodes underneath the one specified target to seed the Ajax spider.
- Context Name : (Optional) The name for any defined context. If the value does not match a defined context then an error will occur.
This configuration section includes the parameters that need to be sent to perform the active scan against the target.
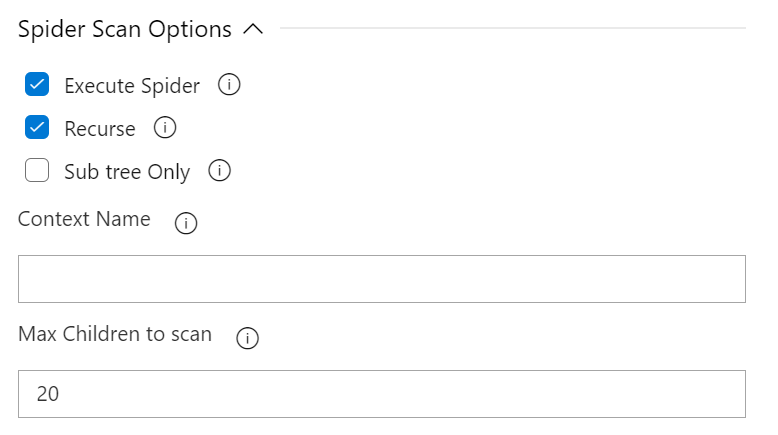
- Execute Spider Scan : Enable to run a spider scan on the target.
- Recurse : (Optional) Enable to use the nodes underneath the one specified target to seed the spider.
- Subtree Only : (Optional) Enable to restrict the spider under the target url subtree.
- Context Name : (Optional) The name for any defined context. If the value does not match a defined context then an error will occur.
- Max Children : (Optional) Set to limit the number of children scanned.
This configuration section includes the parameters that need to be sent to perform the active scan against the target.
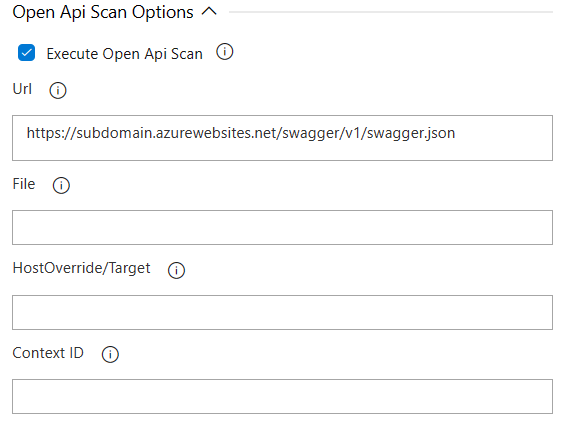
- Execute Open Api Scan : Enable to run a Open Api scan on the target.
- Url : Enter data in URL or File. Not both. Url: The URL locating the OpenAPI definition. The url must exist and be accessible from the server running ZAP. If not, it will give an error. https://www.zaproxy.org/docs/desktop/addons/openapi-support
- File : Enter data in File or URL. Not both. The file that contains the OpenAPI definition. https://www.zaproxy.org/docs/desktop/addons/openapi-support
- HostOverride/Target : (Optional) HostOverride: The Target URL (called hostOverride for historical reasons) to override the server URL present in the definition. Target: The Target URL to override the server URL present in the definition. https://www.zaproxy.org/docs/desktop/addons/openapi-support
- Context ID : (Optional) Scan context identifier. https://www.zaproxy.org/docs/desktop/addons/openapi-support
This configuration section includes the parameters that need to be sent to perform the active scan against the target.
- Execute Active Scan : Enable to run an active scan on the target.
- Context ID : (Optional) Context identifier of the Scan context.
- Recurse : (Optional) Set recurse option to scan URLs under the given target URL.
- In Scope Only : (Optional) Set In Scope only to true to constrain the scan to URLs that are in scope (ignored if a Context is specified).
- Scan Policy Name : (Optional) Scan Policy Name allows to specify the scan policy (if none is given it uses the default scan policy).
- Method : (Optional) Allow you to select a given request in conjunction with the given URL.
- POST Data : (Optional) Allow you to select a given request in conjunction with the given URL.
This configuration section includes the parameters that need to be sent to perform the active scan against the target.
- Enable Verifications: Enable to add thresholds for security risk types and fail the build if the threshold is exceeded.
- High Risk Alert Threshold: Maximum number of allowed High Risk Alerts. The build will fail if the number of high risk alerts equals or exceeds this threshold.
- Medium Risk Alert Threshold: Maximum number of allowed Medium Risk Alerts. The build will fail if the number of medium risk alerts equals or exceeds this threshold.
- Low Risk Alert Threshold: Maximum number of allowed Low Risk Alerts. The build will fail if the number of low risk alerts equals or exceeds this threshold.
This configuration section includes the parameters that need to be sent to perform the active scan against the target.
- Report Type : Select the type of report you want generated. Available types are HTML, XML, Markdown or All.
- Destination Folder : The destination folder that the report file is created. You can use variables. Eg. $(agent.builddirectory).
- Report Filename : Name of the report file, without the extension. Extension is determined by the Report Type. Eg. OWASP-ZAP-Report-2017-00-00.
On Windows servers you can complement the use of this extension with:
https://marketplace.visualstudio.com/items?itemName=solucionespsg.OwaspZapOnPremiseStartStop
With this extension you will be able to remotely start a new Owazap session on a new port, scan the URL and then stop the started session.
Welcome to the Owasp Zap Scanner for Azure DevOps repository! This repository is designed to help you get started with using the Owasp Zap Scanner tool in your Azure DevOps pipeline. In this README, you will find information on how to contribute to this project, as well as how to use the tool in your pipeline.
If you find a bug, please check the currently listed Issues [^1^][1]. If the bug is not listed, please open a new issue [^1^][1] and include a detailed description of the bug.
If you have fixed a bug, please open a new pull request with the fix.
If you would like to add or suggest a new feature, or change an existing one, please open a new issue [^1^][1] and include a detailed description of the feature or change.
We welcome contributions from the community! To contribute to this project, please follow these guidelines:
- Fork this repository.
- Create a new branch for your changes.
- Make your changes and commit them to your branch.
- Push your changes to your forked repository.
- Open a new pull request with your changes.
A special thanks to all the contributors [^1^][1] who have helped make this project possible.